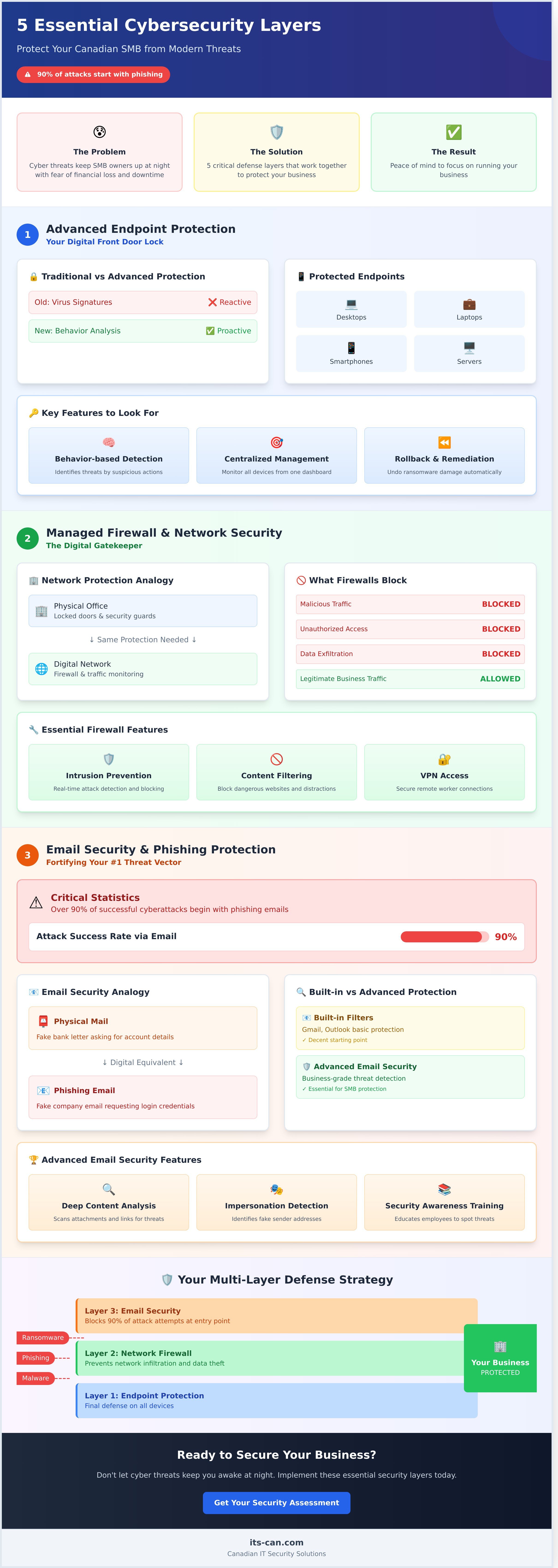
keep you up at night? For many Canadian small business owners, navigating the world of cyber threats feels overwhelming. It’s a confusing maze of technical jargon and expensive tools, leaving you unsure of where to even begin to feel properly protected. You just want peace of mind, but the constant risk of financial loss and costly downtime is a major source of stress.
It’s time to put an end to that frustration, finally and forever. You don't need a massive IT budget or a degree in computer science to secure your company. You just need a clear, straightforward plan. We’ve designed this guide to give you exactly that, breaking down the essential cybersecurity solutions in plain English. We will show you the five critical layers of defence you need to implement to safeguard your data, your finances, and your reputation, so you can get back to focusing on running your business.
1. Advanced Endpoint Protection: Your Digital Front Door Lock
Think of your company’s security like your front door. For years, a simple key lock-like traditional antivirus software-was good enough. But today’s cybercriminals use sophisticated tools to bypass old-school defenses. Relying on outdated software is like using a simple padlock to protect a bank vault; it just won’t stand up to a modern attack.
This is where Advanced Endpoint Protection (AEP) comes in. It’s the modern smart lock system for your digital world, acting as both the first and last line of defense. An 'endpoint' is simply any device that connects to your network-from office PCs and laptops to the smartphones your team uses on the go. Protecting every single one is no longer optional; it's essential.
What It Is (In Plain English)
Forget the old way of just checking for a list of known viruses. AEP is intelligent security software installed on all your company devices that actively watches for suspicious behavior. This proactive approach adheres to core cybersecurity principles by focusing on how threats act, not just what they look like. This is the key to stopping new, never-before-seen threats like zero-day attacks and sophisticated ransomware before they can cause devastating damage.
Why Your SMB Needs It
Is the thought of a ransomware attack locking up all your critical files keeping you up at night? With a distributed workforce, your business is more vulnerable than ever. AEP is one of the most critical cybersecurity solutions because it protects your team wherever they work. It secures remote workers' laptops far from the safety of the office firewall and prevents a simple mistake-like an employee accidentally clicking a malicious link-from turning into a costly, business-halting disaster.
Key Features to Look For
When evaluating AEP platforms, focus on these three non-negotiable features that deliver real peace of mind:
- Behavior-based Threat Detection: This is the "smart" part of the system. It identifies and blocks malicious activity based on suspicious actions, rather than relying on outdated signature lists.
- Centralized Management Console: Get a bird's-eye view of every protected device from a single dashboard. This allows your IT partner to monitor threats, update policies, and respond to incidents instantly, without chasing down individual computers.
- Rollback and Remediation: In a worst-case scenario where a ransomware attack begins, this feature can act like a time machine, reverting infected files to their clean, pre-attack state and undoing the damage.
2. Managed Firewall & Network Security: The Digital Gatekeeper
Think of your company’s network as your digital office building. It’s where your team works, where you store valuable client data, and where your most critical operations happen. Now, would you leave the front door of your physical office unlocked and unguarded? A managed firewall is the professional security guard for your digital office, standing watch 24/7 at the main entrance. It actively inspects every piece of data coming in and going out, ensuring only safe, authorized traffic gets through. This is far more advanced than the basic router your internet provider gave you; it's a dedicated security appliance built to protect your business.
What It Is (In Plain English)
In the simplest terms, a firewall is a protective barrier that sits between your internal business network and the wider, often hostile, internet. It's a set of rules and technologies that acts as a filter. Its primary job is to block malicious traffic, viruses, and unauthorized access attempts from ever reaching your computers and servers. Just as importantly, it can be configured to prevent sensitive company or client data from being sent out of your network without permission, stopping a potential data breach in its tracks.
Why Your SMB Needs It
For any Canadian small or medium-sized business, a weak network perimeter is an open invitation for disaster. Without a robust firewall, hackers can gain direct access to your servers, deploy ransomware, and steal confidential information. Building a secure perimeter is a core principle of the cybersecurity basics, which provides actionable guidance for businesses of all sizes. A managed firewall is one of the most cost-effective cybersecurity solutions because it proactively eliminates threats, preventing costly downtime and reputational damage before they can impact your ability to serve your customers.
Key Features to Look For
When evaluating modern firewall and network cybersecurity solutions, don't settle for the basics. Look for a managed service that includes these critical features to give your business the peace of mind it deserves:
- Intrusion Prevention System (IPS): This goes beyond simply blocking known threats. An IPS actively analyzes network traffic for suspicious patterns and can shut down an attack in real-time as it’s happening.
- Content Filtering: Allows you to block employees from accessing dangerous or non-productive website categories, reducing the risk of malware infections and keeping your team focused.
- Virtual Private Network (VPN): Provides a secure, encrypted tunnel for your remote and travelling employees to connect to the office network, ensuring company data is protected no matter where they are.
3. Email Security & Phishing Protection: Fortifying Your #1 Threat Vector
Are you ready for a sobering fact? Over 90% of all successful cyberattacks begin with a simple phishing email. That one message, disguised as a legitimate request, is the primary way criminals get inside your network. While the built-in filters from services like Gmail or Microsoft 365 are a decent starting point, they are simply not powerful enough to protect a business from today’s sophisticated threats.
Think of a phishing attack like receiving a fake letter in the mail that looks exactly like it’s from your bank, asking you to confirm your account details and password. An advanced email security solution acts as a dedicated, expert screening service that inspects every single piece of digital mail for signs of fraud before it ever reaches your team’s inbox, preventing a costly mistake.
What It Is (In Plain English)
This is a specialized security layer that sits between the internet and your employees' inboxes. It proactively scans every incoming email for red flags that standard filters miss. Using advanced artificial intelligence (AI), it looks for forged sender addresses, malicious links hidden behind friendly text, infected attachments, and subtle signs of impersonation fraud. It’s the digital equivalent of a security guard for your company’s mailroom.
Why Your SMB Needs It
One wrong click by a well-meaning employee can lead to catastrophic data loss, financial theft, or costly downtime. This solution directly prevents the most common and damaging email-based attacks. It stops Business Email Compromise (BEC), where a hacker impersonates the CEO to request an urgent wire transfer, and it blocks access to fake login pages designed to steal company passwords. Protecting your inbox is a foundational part of modern business security, a principle that aligns with CISA's guidance for SMBs on creating a culture of security awareness.
Key Features to Look For
When evaluating these essential cybersecurity solutions, ensure the service includes these non-negotiable features:
- Link Scanning and Sandboxing: Checks where links actually go before a user can click them and opens attachments in a safe, isolated virtual environment to see if they are malicious.
- Impersonation and Spoofing Detection: Uses AI to identify when an email is pretending to be from a trusted source, like a senior executive or a key vendor.
- Advanced Malware and Spam Filtering: Goes beyond basic keyword filtering to block sophisticated ransomware, spyware, and persistent spam campaigns.
4. Data Backup & Disaster Recovery: Your Ultimate Safety Net
What happens if your business is hit by a devastating ransomware attack tomorrow? Or if a server fails, a fire breaks out, or a critical laptop is stolen? Many business owners think of cybersecurity as a wall to keep threats out. But the best cybersecurity solutions include a plan for when a threat gets through. Data Backup and Disaster Recovery is your ultimate safety net-an 'undo' button that ensures a catastrophic event doesn't put you out of business for good. It’s not just about security; it’s about business continuity.
What It Is (In Plain English)
Forget the tech jargon. A simple backup is just a secure copy of your data. A full Disaster Recovery plan, however, is the crucial next step: it’s the tested, step-by-step playbook for restoring that data and getting your entire operation back online quickly. Think of it as the difference between having a spare tire in your trunk and having a full roadside assistance plan that changes it for you, day or night.
Your Guaranteed Escape from Ransomware & Other Disasters
Let's be direct: a robust, isolated backup is your only guaranteed way to recover from a ransomware attack without paying the criminals. When they lock your files and demand thousands in untraceable currency, you can confidently refuse, wipe the infected systems, and restore your clean data from a point before the attack happened. But its value extends far beyond cybercrime. A proper recovery plan also protects you from:
- Hardware Failure: Servers and hard drives don't last forever. A failure can wipe out years of essential data instantly.
- Human Error: Accidents happen. An employee might accidentally delete a critical folder or overwrite an important file.
- Physical Disasters: A fire, flood, or theft at your Canadian office can destroy your onsite equipment and the data on it.
To ensure your plan works when you need it most, it must be built on proven principles. Look for professional services that include automated, frequent backups following the "3-2-1 Rule" (3 copies, 2 media types, 1 offsite) and, most importantly, regular testing to prove your data is fully recoverable. This isn't an IT luxury; it's an essential investment in your business's survival and your peace of mind.
5. Security Awareness Training: Empowering Your Human Firewall
You can invest thousands of dollars in firewalls and advanced software, but what happens when a clever phishing email bypasses it all and lands in an employee's inbox? The frustrating truth is that technology alone is not enough to stop every attack. Cybercriminals are increasingly targeting your staff, knowing that a single human error can unlock your entire network. This is where your team transforms from a potential vulnerability into your most powerful security asset.
Effective Security Awareness Training is one of the most critical cybersecurity solutions for any Canadian SMB. It’s not about buying more hardware; it’s about empowering your people with the knowledge to defend your business from the inside out. A well-trained employee can spot and report a suspicious email that even the most advanced filter might miss, effectively creating a "human firewall" that protects your sensitive data.
What It Is (In Plain English)
Think of it as ongoing driver's education for the digital world. This solution provides regular, simple-to-understand training for your entire staff on how to recognize modern cyber threats. It often includes simulated phishing tests-safe, controlled fake attacks-to see how your team responds in a real-world scenario. The goal is to build good habits around password creation, data handling, and how to report a security incident without panic.
Why Your SMB Needs It
Ignoring the human element of security is a costly mistake. By investing in training, you turn your employees from a common target into your first line of defense. This simple shift drastically reduces the success rate of phishing and social engineering attacks, which are the leading causes of data breaches for small businesses. More importantly, it fosters a strong, security-conscious culture where everyone feels responsible for protecting the company.
Key Features to Look For
When evaluating these essential cybersecurity solutions, look for a program that your team will actually use. Steer clear of long, boring videos and seek out platforms that offer:
- Engaging, bite-sized training modules that can be completed in just a few minutes.
- Regular, automated phishing simulations with clear reporting to track progress and identify areas for improvement.
- Comprehensive topic coverage, including phishing, password security, ransomware, and even physical security best practices.
Ready to build a stronger, more resilient team? Discover how our training programs can empower your human firewall.
Bringing It All Together: A Managed Approach to Cybersecurity
You now have a list of the top five security tools essential for protecting your Canadian business. But implementing them is only half the battle. Purchasing five different products, configuring them correctly, and monitoring them around the clock can quickly become a complex, costly, and overwhelming task-one that pulls you away from your actual business.
A truly effective defence isn't just about having the right tools; it's about having them work together as part of a unified strategy. This is where a managed approach to your cybersecurity solutions transforms your protection from a collection of parts into a seamless, proactive shield.
The Problem with a DIY Approach
Trying to manage your own cybersecurity can feel like a losing battle. When you patch together different products from different vendors, dangerous security gaps can form between them. Who is monitoring the flood of alerts from five separate systems? Is it you, after a long day of serving customers? Keeping up with the constant evolution of cyber threats is a full-time job, and a single missed alert or misconfigured setting can leave your business exposed.
Benefits of a Managed Security Partner
Instead of juggling multiple vendors and constant alerts, a managed security partner provides a single, expert team to handle everything. This approach offers a powerful, stress-free way to secure your business and finally gain peace of mind. Key benefits include:
- 24/7 Expert Monitoring: One dedicated team of security professionals manages all your security layers, 24/7/365. We watch for threats so you don’t have to.
- Affordable Enterprise-Grade Tools: Gain access to best-in-class cybersecurity solutions and expertise that would otherwise be prohibitively expensive, all for a predictable monthly cost.
- A Holistic, Unified Defence: We ensure all your security tools work together seamlessly, eliminating the dangerous gaps left by a DIY approach and creating a stronger, more resilient defence.
- Freedom to Focus on Your Business: Stop worrying about IT nightmares. Let us handle your security, so you can focus on what you do best.
Take Control of Your Security with a Proactive Partner
Protecting your business in 2026 requires more than a single piece of software. True security comes from a multi-layered strategy that combines robust technology-like endpoint protection and managed firewalls-with empowering your team through security awareness training. Juggling these essential cybersecurity solutions can feel overwhelming, but you don’t have to do it alone.
As your dedicated, Toronto-based cybersecurity experts, we provide the proactive, 24/7/365 network monitoring your business deserves, giving you complete peace of mind. We handle all the complexity and explain everything in Plain English-that’s our no-geek-speak promise. It’s time to solve your IT nightmares once and for all so you can focus on your business.
Are you ready to secure your company's future? Book a Free, No-Obligation Cybersecurity Consultation Today. Take the first step towards a more secure, productive, and stress-free operation.
Frequently Asked Questions About Cybersecurity
What is the difference between antivirus and modern endpoint protection?
Think of traditional antivirus as a security guard with a list of known troublemakers-it only stops threats it already recognizes. Modern endpoint protection is a proactive security team that analyzes suspicious behaviour to stop new and unknown threats, like ransomware, before they cause damage. It provides a much higher level of security necessary to defend against today's sophisticated cyberattacks.
Do we still need a firewall if our team works from home?
Yes, absolutely. A traditional firewall only protects your office, not your employees' home networks. With a remote team, your business is exposed through every home internet connection. Modern cybersecurity solutions protect each individual device, no matter where it is, creating a secure perimeter around your entire team. This ensures your critical business data remains safe, even with a distributed workforce.
How much should a small business budget for cybersecurity services?
For small and medium-sized businesses in Canada, a realistic budget for comprehensive, managed cybersecurity services typically falls between C$100 and C$250 per employee per month. This proactive investment is far less than the devastating cost of a single data breach. A predictable monthly fee gives you peace of mind and allows you to focus on your business, knowing you are protected by experts.
Isn't the security included with Microsoft 365 or Google Workspace enough?
While the built-in security is a good starting point, it is not enough to fully protect your business. These platforms are the top targets for cybercriminals who design attacks specifically to bypass those default protections. To be truly secure, you need layered, professional-grade security that defends against advanced threats like targeted phishing, business email compromise, and sophisticated malware.
What is the single most important first step to improving our security?
The most critical first step you can take is to implement Multi-Factor Authentication (MFA) across all your accounts, especially for email. MFA requires a second verification step, like a code sent to a phone, before granting access. This simple, low-cost measure is your strongest defence against account takeovers, even if a cybercriminal manages to steal an employee's password.
Can't I just buy these solutions myself? Why do I need a service provider?
While you can purchase security tools, implementing and managing them effectively requires constant monitoring and deep expertise. Cyber threats evolve daily. A dedicated service provider gives you a team of certified experts who handle the 24/7 monitoring, updates, and response for you. This frees you from the stress of managing complex technology and lets you focus on what you do best-running your business.